HTB Business CTF 2022 - Operator
This challenge use awx-operator in kubernetes cluster

Full time job to handle operational private cloud. In spare time love to building and breaking stuff 👀
Cover Illustration source https://www.pixiv.net/en/artworks/89193760
Alright, let’s continues to 2nd challenge called Operator. Here is the challenge description:
We have located Monkey Business operator blog where they are leaking personal informations. We would like you to break into their system and figure out a way to gain full control.
Just like previous challenge we only got an IP address. So i just running Nmap to scan the IP address to know what services are running and in which port.

The scan result show there is 6 open ports:
22 - ssh
80 - http
3000 - ppp
8443 - https (most likely kube api server)
10250 - http (most likely kubelet)
30080 - http nginx
Let’s explore each services one-by-one
- 80 - Web server
Access from browser we got website page like this.
.png)
After check all posts on the website, there is one post that provide a link that leads to port 3000. Let’s visit that link.
.png)
- 3000 - gogs (self-hosted git server)
The link that we found earlier leads us to git repository.
.png)
Since the repository itself seems not have useful information i tried to explore the gogs server to find another repository.
Yeah, there another repository named awx-operator
.png)
Explore the repository and i found a closed issue. That issue mentioned another repository called awx-k8s-config.
.png)
Then i open the repository and try to explore the files stored in the repository. Seems like the files stored in the repository are manifest file to deploy awx-operator in kubernetes. From commit history i found credentials for login to awx operator dashboard
.png)
- 30080 - Awx dashboard
Login to awx dashboard using credentials we got before, here the dashboard look like.
.png)
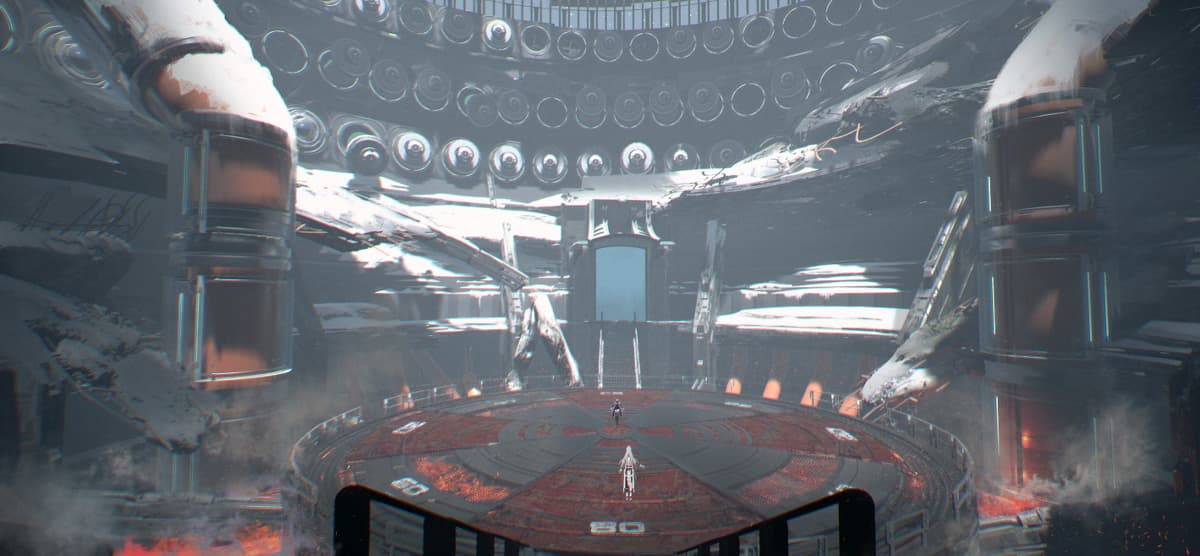
Briefly, how awx work is awx will deploy pod in kubernetes cluster then make it as runner to to run ansible playbook. So, we can simple create our own ansible playbook to get kubernetes serviceaccount token that we can use to access kubernetes cluster.
First, we create new user and repository on gogs server. Then we stored our ansible playbook that print serviceaccount token that stored in file /var/run/secrets/kubernetes.io/serviceaccount/token inside the pod. Here the playbook that i use.
.png)
Then on awx dashboard we create new project that use our new repository as source control.
.png)
Then we create new job template for the project to run ansible playbook.
.png)
Then we run the job, but i got an error. Seems like the file that contain serviceaccount doesn’t exist in the runner pod.
.png)
After explore a while i found that the pod spec that deploy as runner has automountServiceAccountToken option set to false. We need to change that option to true. The configuration can found in Instance Group -> choose group -> customize pod configuration.
.png)
Then re-run the job we’ve created. Now finally we got the serviceaccount token.
.png)
Next we use that token to access the kubernetes cluster with kubectl.
.png)
When i tried to list pods running got error permission. Seems like our token doesn’t has such permission, since we use the default serviceaccount. Well we change it but first we need to know what serviceaccount that exist in the cluster. We can open awx-operator.yaml file in awx-k8-config repository to see that we can use awx-operator-controller-manager serviceaccount.
.png)
To make it our runner pod using that serviceaccount we need to set option serviceAccountName in pod configuration.
.png)
Re-run the job to get new token from new serviceaccount
Then try run kubectl using new token, here i check the permission we got.
.png)
Seems like now we can create new pod. Since the flag.txt file are stored in the host machine we can create pod that mount / host machine to the pod, so we can read the flag.txt. Here the pod manifest that i use.
.png)
Next just create the pod and exec shell inside pod then read the flag.txt file.
.png)
Reference: